Reliable Access Control Systems Installation & Service in the NYC Metro Area
Hire the Best Access Control Installation & Support Company in NYC
Contact Us
✔ Contact Us

Reliable & Trusted Access Control System Installation & Support In the NYC METRO AREA

Streamline Telecom is proud to have installed or serviced access control systems at some of the most iconic locations in the greater NYC area, including Queens Hospital, Elmhurst Hospital, Yahoo, DAZN, Touro College, One World Trade Center, and Newark Airport.
Unlike many contractors working in the city, we hold both a New York State Security License (required by law to work on access control systems) and a BICSI RDD Certification, the highest standard of certification in our industry.
Whether your project is big or small, our team has the expertise to get the job done correctly and on time.
"They all put their heart and soul into every job that they do."
Contact us now to get a project assessment and quote, or read on to learn about selecting the perfect access control system for you, including types of systems, major manufacturers of systems, and answers to frequently asked questions.
The Essentials of Access Control Systems
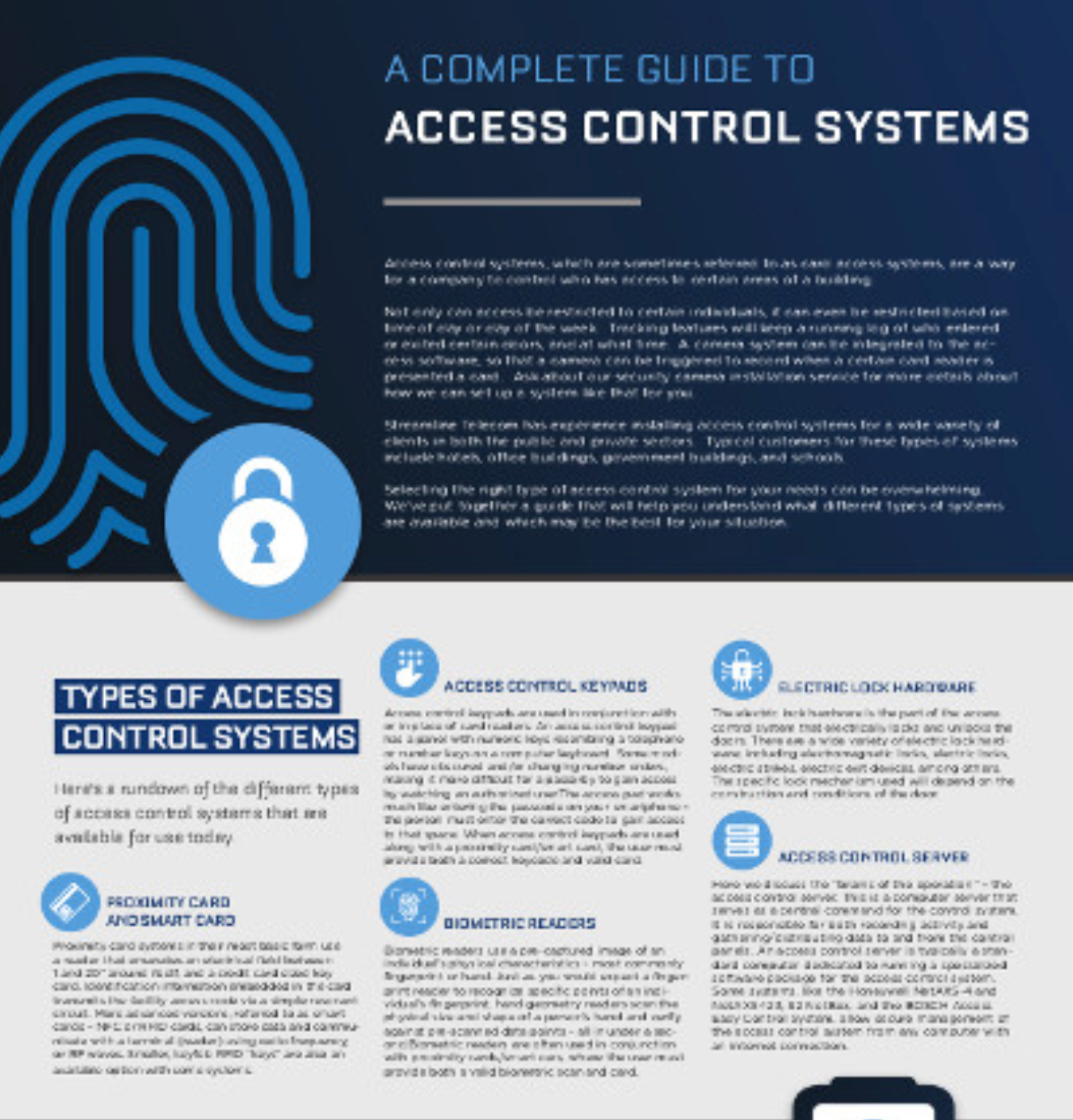
Access control systems, which are sometimes referred to as card access systems, are a way for a company to control who has access to certain areas of a building.
Not only can access be restricted to certain individuals, it can even be restricted based on time of day or day of the week.
Tracking features will keep a running log of who entered or exited certain doors, and at what time.
A camera system can be integrated to the access software, so that a camera can be triggered to record when a certain card reader is presented a card. Ask about our security camera installation service for more details about how we can set up a system like that for you.
Get Our Simple Infographic to Help You Select the Perfect Access Control System
Selecting the right type of access control system for your needs can be overwhelming. We’ve put together a guide that will help you understand what different types of systems are available and which may be the best for your situation.
Streamline Telecom has experience installing access control systems for a wide variety of clients in both the public and private sectors. Typical customers for these types of systems include hotels, office buildings, government buildings, and schools.
Explore Our Complete Guide to Access Control Systems
✔ Types of Access Control Systems
 Cntact Us
Cntact UsProximity Card and Smart Card
Proximity card systems in their most basic form use a reader that emanates an electrical field between 1 and 20” around itself, and a credit card sized key card. Identification information embedded in the card transmits the facility access code via a simple resonant circuit. More advanced versions, referred to as smart cards – NFC or RFID cards, can store data and communicate with a terminal (reader) using radio frequency, or RF waves. Smaller, keyfob RFID “keys” are also an available option with some systems.
Access Control Keypads
Access control keypads are used in conjunction with or in place of card readers. An access control keypad has a panel with numeric keys resembling a telephone or number keys on a computer keyboard. Some models have obscured and/or changing number orders, making it more difficult for a passerby to gain access by watching an authorized user.The access pad works much like entering the passcode on your smartphone – the person must enter the correct code to gain access to that space. When access control keypads are used along with a proximity card/smart card, the user must provide both a correct keycode and valid card.
Biometric Readers
Biometric readers use a pre-captured image of an individual’s physical characteristics – most commonly fingerprint or hand. Just as you would expect a fingerprint reader to recognize specific points of an individual’s fingerprint, hand geometry readers scan the physical size and shape of a person’s hand and verify against pre-scanned data points – all in under a second.Biometric readers are often used in conjunction with proximity cards/smart cars, where the user must provide both a valid biometric scan and card.
Electric Lock Hardware
The electric lock hardware is the part of the access control system that electrically locks and unlocks the doors. There are a wide variety of electric lock hardware, including electromagnetic locks, electric locks, electric strikes, electric exit devices, among others. The specific lock mechanism used will depend on the construction and conditions of the door.
Access Control Server
Here we discuss the “brains of the operation” – the access control server. This is a computer server that serves as a central command for the control system. It is responsible for both recording activity and gathering/distributing data to and from the control panels. An access control server is typically a standard computer dedicated to running a specialized software package for the access control system. Some systems, like the Honeywell NetAXS-4 and NetAXS-123, S2 NetBox, and the BOSCH Access Easy Control System, allow secure management of the access control system from any computer with an internet connection.
✔ Components of Access Control Systems
 Contact Us
Contact UsAccess control systems consist of 4 main components – a credential, a reader, a magnetic lock, and a computer control system.
Credential: A credential can easily be defined as a unique identifier – whether it be an object (such as a card or keyfob) a piece of information (such as a keycode) or a biometric feature (like a fingerprint or hand shape) or some combination of any of these.
Reader: The reader can be a keypad, a card reader, or a biometric reader, but its basic function is to send a card number to an access control panel, which will then verify the number against a previously-entered access list.
Magnetic lock: The magnetic lock typically controls the only entry of the access control system; it acts much like the magnet on your refrigerator door, holding it closed.
Computer control system: This piece acts as the system’s “brain,” controlling the central database as well as the file manager for the system. It will record the system activity and distribute the required info to the access control system panels..
✔ Common Features of Access Control Systems
 Contact Us
Contact UsEase of Use and Flexibility
Having a control system in place that is difficult to use can be a huge time and energy waster. Choose an access control system that is both easy to use and powerful enough to handle your access control needs. Having the ability to easily make changes to cardholder records and run report data is key.
Integration
Some access control systems can be integrated with other security protocols, such as intrusion alarms and video systems, so everything can be managed with one software solution – simplifying the management of all three.
Backups and Reporting
You’ll want to choose a system that offers the level of reporting data that is right for your organization. A good access control system will essentially keep a log of who was where, when – a database will store all card and key-in data per entry point with the time and date. This goes back also to ease of use, but running a detailed report of the log data easily should be a priority. If you need to know who went through door B at 10pm last Tuesday, it should be easy to find that information, and quickly.
Gathering this data is for nothing if it is not backed up regularly. Be sure your access control system software either has an integrated scheduled backup or have a secondary backup system in place.
Operational Efficiency
Employees typically don’t need any special training on the use of electronic lock systems, and employers don’t have to contend with rekeying locks when an employee loses, breaks, or steals a hard key. Employees don’t need to worry about a handful of keys and keeping track of which key works for what. Administration is typically straightforward and convenient – access privileges can be added, modified, or revoked quickly as needed.
Improved Customer Experience
Electronic access systems allow the sales force, bank personnel, nurses and pharmacists to access restricted items more immediately, without making the consumer wait while items are retrieved by the one person with a hard key. Customer satisfaction increases while customer turnover time decreases.
FREQUENTLY ASKED QUESTIONS
About Our Access Control Systems in the NYC Metro Area
Where can an Access Control System be used?
It can be used on one door or all the doors in your office, depending on your particular security needs. If you don’t have increasing levels of security throughout your organization, an access control system on your main entrance will allow employees to enter without the inconvenience of issuing keys.
Will I have to replace my doors to accommodate these special locks?
No, in most cases, a door that is secure with a standard hard key system is sufficient and adaptable to electronic lock systems. We’ll make sure any modifications needed are made at the time of installation.
Will my employees need special training to operate an Access Control System?
Employees using the electronic access system won’t need any extensive training. Once their credential has been set up, using these systems is fairly intuitive – as simple as swipe, tap, enter a passcode or a combination thereof.
Depending on the scope of your facilities’ needs, administering the access control system can vary in difficulty. Learning to manage users, set up access, etc. can be as simple as following basic tutorials (this is the case for most small business applications) to attending training held by the software company you choose to work with.
What happens if a card is lost?
Fortunately, each card is individually coded. If one employee loses or damages theirs, then that card can be deleted without impacting any other card. You can simply issue a new one to the employee.
Will this improve my business’s risk management strategy?
Yes. Employees can easily forget to re-lock a door or cabinet after they move on to another task or space. This can leave sensitive data open to potential theft; and in the case of critical infrastructure and healthcare providers – hefty government fines.
Is it difficult to install?
Streamline Telecom has experience installing access control systems for a wide variety of clients. Any business or agency that has areas that hold confidential information, critical infrastructure, patient data, accounting information, or expensive equipment should consider an access control system – this includes law firms, hospitals and clinics, investment firms, school systems, law enforcement and government agencies, public utilities, and really, any business that deals with sensitive information.
Although electronic access control systems and their various components can seem complicated, Streamline Telecom is here to help find the right access control and security solutions to fit your needs. Call us today or request a quote online to get started!